|
|
|
PHONE TAPPING, BUGGING & HACKING.
 IS YOUR PHONE SPYING ON YOU........??????? IS YOUR PHONE SPYING ON YOU........???????
A version of the GhostCtrl BACKDOOR SPYWARE APP has been released which gives anyone the potential to SPY on and HACK INTO your MOBILE PHONE.
The spyware app can be remotely installed on to your mobile device disguised within an email or text message with a link.
The app is not visible on the phones screen and runs in the background at all times.
The spy app allows any one who has your telephone number to,,
Read all your text messages.
Read all your emails.
Listen to any voice messages.
View all your photos.
Upload your entire address book.
Track your phones location world wide.
Listen to any live conversation within 5 meters of your phone at any time. And more !!
EAVESDROPPING AND ROOM HACKING.

The latest GSM mobile phone technology now gives a box the size of a golf ball fitted with a standard mobile SIM card the ability to,,,
Listen in to any voice conversations within a room.
Listen to any telephone conversations within a room.
Video any activity within a room.
Record any of above for up to 28 days.
If no mobile GSM service is available a wireless connection for the above can be made to any local WI FI network.
This enables any one with a MOBILE DEVICE or PC to remotely monitor and play back any of the above from any where in the world.
The room hacking and remote surveillance devices can be easily hidden into every day objects and powered from internal batteries or mains charging adapters.
The devices are available from internet security shops from £50.
Mobile surveillance devices can also be concealed within a vehicle.
They can operate from internal batteries for up to 12 months or constantly from the vehicles own battery.
This enables any one with a smart phone to track and monitor the vehicles location any where in the world.
Any voice or telephone conversations from within the vehicle can also be monitored at any time.
TO COMBAT THE ABOVE THREATS ALARMSPY HAS DEVELOPED THE FOLLOWING COUNTER SURVEILLANCE PRODUCTS.
 UNIVERSAL RF SURVEILLANCE DETECTOR PRICE £164 UNIVERSAL RF SURVEILLANCE DETECTOR PRICE £164
Comprises of an easy to use hand held detector which alerts the user to the presence of any RADIO TRANSMITTING jamming devices, phone taps, bugging devices, spy cameras, tracking devices or if any mobile phone is actively being hacked into.
OPERATION:
The radio surveillance detector operates from internal rechargeable batteries or mains adapter.
The detector has a variable sensitivity alarm which will sound if any transmissions from wireless camers, bugs, phone taps or trackers are detected up to a distance of 5 meters.
A signal strength meter enables the exact position of the transmission to be located.
If the detector is placed in the centre of a room and any mobile phone in the room gets hacked into, the detector will go into alarm and the particular phone can be identified using the signal strength meter.
Also incorperates:
Optical lens finder to detect hidden surveillance cameras in a room or concealed in every day items which may be dormant or not transmitting a radio signal.
Infra red light detector to locate any hidden infra red cameras opperating at night.
Magnetic field detector to locate magnetic tracking devices hidden on vehicles.
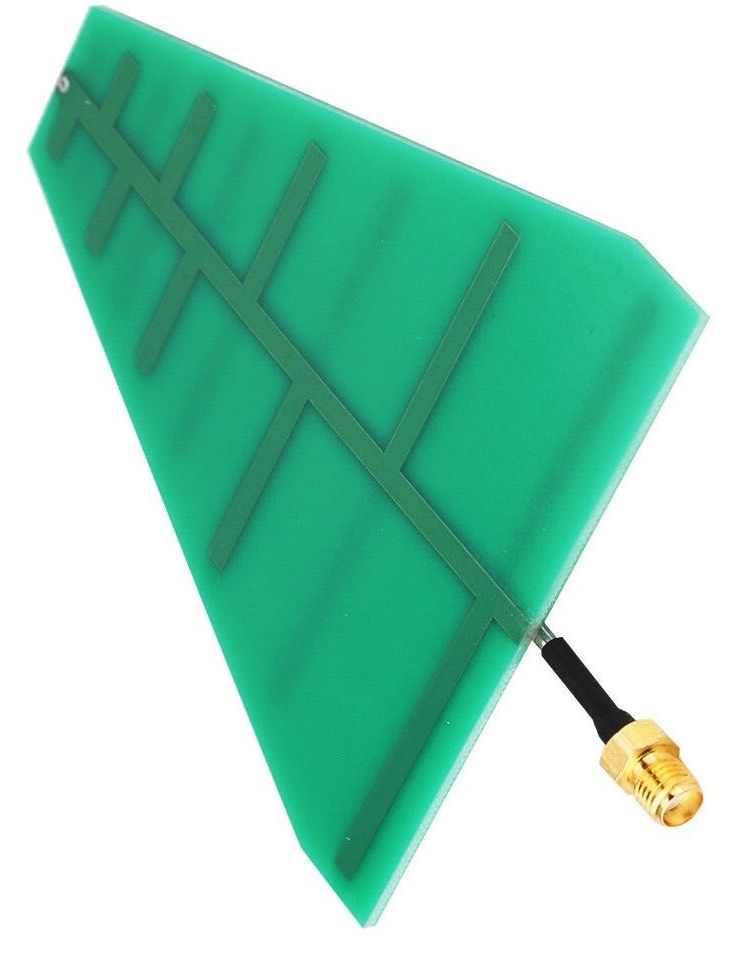 Supplied with mini direction finding antenae to locate any transmitting surveiilance device or radio jamming device at a distance or hidden externally in undergrowth or bushes. Supplied with mini direction finding antenae to locate any transmitting surveiilance device or radio jamming device at a distance or hidden externally in undergrowth or bushes.
The directional antenae will also locate drones or drone remote control transmitters operating in the imideate vicinity.
The antenae connects to the top of the detector and will increase the receiving sensitivity in the forward direction only.
This can also help accurately locate all types of surveillance transmitters with low power output.
High power devices can also be located by adjusting the RF sensitivty.
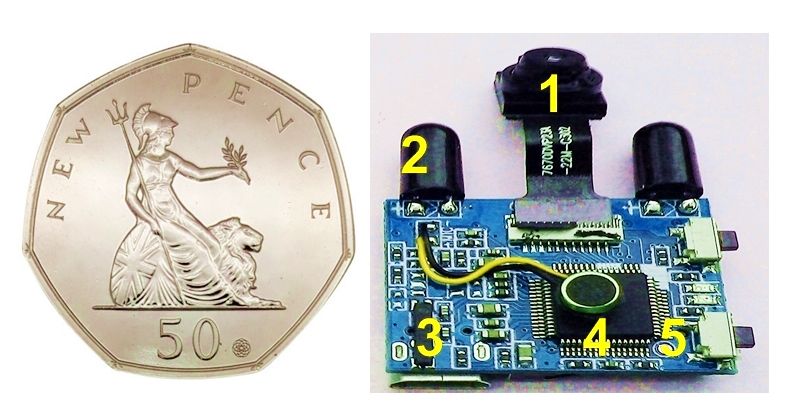 Supplied with a working HD micro infra red Wi Fi camera module as found in many hidden cctv surveillance devices concealed in every day objects such as clocks, lamps, loud speakers, usb chargers etc. As now found in many holiday lets and facilities. Supplied with a working HD micro infra red Wi Fi camera module as found in many hidden cctv surveillance devices concealed in every day objects such as clocks, lamps, loud speakers, usb chargers etc. As now found in many holiday lets and facilities.
1 Pinhole camera lens. 2 Invisible infra red light to enable night vision. 3 Usb power input.
4 Mini microphone. 5 On/off switch.
The camera will help self train the user on how to use the lens finder, infra red detector, and WIFI detector functions of the RF SURVEILLANCE DETECTOR.
The camera module is supplied in a small black box and can be used as a security device to record any activity within a room with motion detection and remote monitoring on any mobile device.
 Supplied with RF tracking tag to help self train the user in the location of tracking devices. Supplied with RF tracking tag to help self train the user in the location of tracking devices.
The tag can be hidden on a person or vehicle and the user can then learn how to locate it with the above RF SURVEILLANCE DETECTOR.
Bluetooth tracking tags such as Air Tag, Tile and Samsung are very small and easy to conceal in clothing, hand luggage or vehicles.
The tags transmitt a low power signal which is picked up by near by mobile devices which then forwards the location of the signal to the internet cloud.
The tags internal battery lasts for up to 1 year and any mobile device can be used to locate the tag any where in the world via the internet.
All types of tag tracking devices emit a similar signal.
Advanced versions of the RF SURVEILLANCE DETECTOR for higher risk applications available from £280
A complete operational training package is available if required from £100 at our Burton on Trent location or any where in the UK plus travel costs POA.
APPLICATIONS
Detection of RF jamming devices, clandestine listening devices, hidden cameras, tracking devices, and detection of mobile phone hacking in homes, offices, meeting rooms etc.
Will also detect unauthorised use of mobile phones and drones in local prohibited area,s.
Supplied with RF calibration test certificate and user manual.
RF SPECTRUM ANALSER PRICE FROM £600
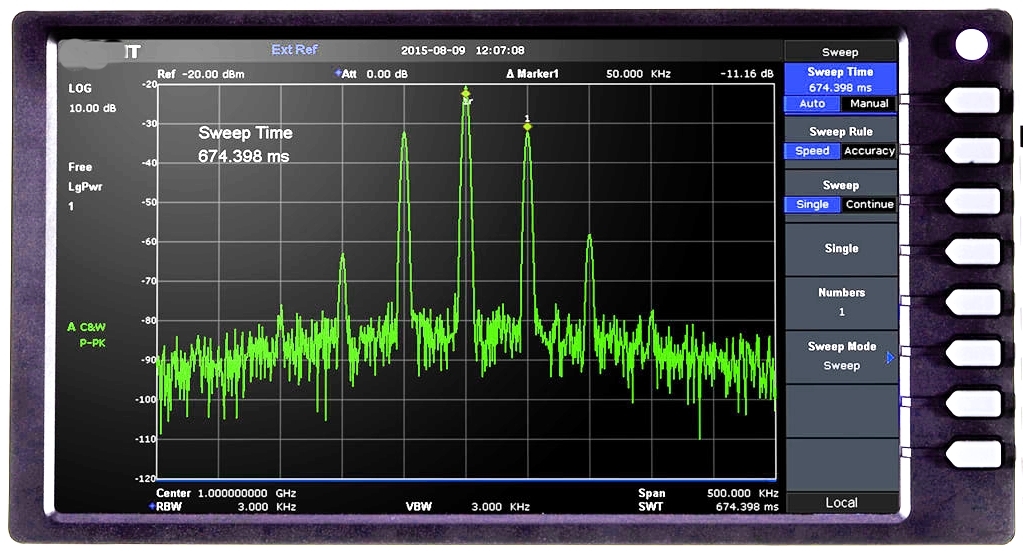
Comprises of a radio frequency spectrum analyzer for electronic counter measures and long range drone detection applications.
OPERATION
The RF Spectrum Analyzer operates from rechargeable battery or mains adapter.
The Analyzer produces an easy to read visual display of the radio spectrum between 1mhz and 6ghz.
The display indicates the presence of all radio transmissions in the immediate area, such as radio and TV broadcasting, two way radio and mobile phone communications. In certain town and city locations these transmissions can be very strong and cause bug detectors and radio interceptors to produce false alarms.
The Spectrum Analyzer will display these transmissions as a constant reference and any new transmissions from bugging devices, cameras or drones that may be remotely controlled will indicate on the screen the moment they become activate.
APPLICATIONS
High risk detection and location of unauthorized radio surveillance devices.
Supplied with a selection of radio surveillance test transmitters and optional training package.
Also available for hire with electronic counter measures engineers to conduct a complete sweep and search of any building or vehicles to detect and locate any unauthorized telephone, audio or video surveillance devices.
 RADIO JAMMERS. RADIO JAMMERS.
A new range of portable radio frequency jammers are now available and although not approved for use in the UK they can be easily obtained over the Internet for less than £100.
The popular models operate at:
433, 434, 868, 900, mhz and 1.8, 2.1, 2.4ghz.
Some of the problems caused by radio jammers:
Wireless burglar alarms, false alarm or 'do not detect' intruders.
Car alarms and door locks will not set or close.
Engines will not start in top of the range vehicles.
GSM security auto dialler's receive no service.
Wireless credit card terminals can not process transactions.
Mobile phones receive no service.
Wifi routers receive no service.
Wireless CCTV systems receive no picture.
Jammers can be easily hidden in nearby locations or vehicles.
The Alarmspy easy to use UNIVERSAL RF DETECTOR is ideal to detect and locate any active local jamming device.
ELECTRONIC, ELECTROMAGNETIC & ACOUSTIC COUNTER MEASURES PRICE FROM £ 675
Comprises of a aluminum brief case incorporating electronic detection equipment to detect, locate and record the presence of electronic surveillance equipment and electronic pain field generators operating in the radio, electromagnetic, sonic and ultrasonic frequency spectrums.
The presence of high power electronic pain fields can cause injury to the human body and can produce a debilitating highly discomforting feeling of nausea, disorientation and paranoia........
The kit comprises of the following..
1 Highly sensitive radio frequency detector which will detect high and low power radio transmissions from 1mhz to 6ghz. Variable sensitivity and led signal strength enables any local transmission source to easily be located. A level control will sound an alarm when any radio transmissions are detected above a preset level. The detector will indicate the presence of microwave and RF pain field generators, audio, video and telephone bugging devices, tracking devices, RF jammers and if a mobile phone is actively being hacked into.
2 Electromagnetic radiation detector which will detect and record dangerous levels of electric and magnetic fields emitting from faulty or modified every day electrical equipment and the presence of electric field pain generators.The detector can also indicate the presence of any paranormal activity.
3 Pre programmed RUGGED 4 inch HD full function mini or 7 inch full size smart phone incorporating the following modifications and apps.
a: Advanced audio spectrum analyzer which scans the entire audio frequency spectrum up to 22khz and displays the frequency and intensity of any sounds or pain fields present in the immediate area. A peak hold function stores on the screen all frequencies that have been detected over a period of time as.This function enables the user to see what sounds have been detected when the user is out or asleep if the analyzer is left on day and night.
b: Sensitive sound meter which will store and display the average and maximum sound levels present in the vicinity in dB over any period of time.
c: Sensitive vibration meter which will store and display the average and maximum building and ground vibrations present in m/s2 over any period of time.
d: Smart audio recorder which operates with the phones built in microphone and records any voices or sounds present in the vicinity over any period of time on to the phones memory for play back and storage for future reference. By enabling the skip silence function the recorder will only record when any sounds above a certain level are detected.
e: Signal generator which will generate low level audio frequencies up to 18kz to test above functions and to enable the user to experience high frequency sound in the pain generator spectrum between 8khz and 17khz. A white and pink noise function is included which can be activated to disable any surveillance microphones present or produce a subtle background sound level.
f: Wi fi monitor analyzer which scans the 2.4ghz and 5 ghz radio spectrum and displays all active Wi Fi devices present in the immediate area including surveillance cameras, routers, PCs etc. A scan function enables the user to see all devices connected to their internet router and identify any unauthorized surveillance devices that may be using the router for remote monitoring of the users premises.
g: Flashlight with strobe light function which will disrupt any unauthorized surveillance cameras operating in the immediate area and locate hidden pinhole lenses. SOS function can also be used as a call for help.
The smart phone also incorporates all standard and internet functions operating on Android with built in Wi Fi, Bluetooth, GPS location, Google, 12MP camera will also operate in the INFRA RED spectrum, and operates with any 2/3/4g sim card.
4 Ultrasonic sound detector and by ten frequency divider enables any sound or pain field generators operating between 10khz and 100khz which is out of the range of human hearing, to be monitored on the internal speaker and displayed on the audio spectrum analyzer.
5 Ultrasonic pain field generator which will generate medium power pain fields with sweep frequencies which can be adjusted between 8khz and 45khz by using the preset control.This enables the above to be tested and for the user to experience medium level sonic and ultra sonic variable pain field frequencies. If set between 14khz and 16khz the output is similar to electronic deterrents used to prevent teenagers from loitering. High power versions as shown below have been used as electronic disruptors to both humans and animals and have been known to cause a horse to throw its rider.
The above kit is supplied with all batteries and chargers ready to go, a technical telephone help line is available to advise users on how to operate the kit and analyze any detected results.
A high risk version incorporating the above with the addition of,, a 6 ghz RF spectrum analyser to monitor high power and low power radio transmisions, geiger counter to detect ionising radiation and radon, thermal imaging microcamera to detect concealed electronic devices and heat sources, air quality analyser to detect air polution particles. The kit is also used to detect the presence of unknown phenomena and UAPs. Price from £2800.
A basic and comprehensive training package on how to get the best out of the counter measures kit is also available, full details on request.
High power ultrasonic and RF pain generators as below are legal in the UK and are available over the internet. They can cause very stressful disturbances to both humans and animals. The presence of these devices can now be detected with the above Electronic counter measures kit.
| | 
|